If you have been looking for ways to ensure your security and privacy online, then you’ve probably heard about Tor and VPN (Virtual Private Networks) services. Both can be described as powerful online tools that enable users to safeguard their information online. While they both serve the same purpose and share many similarities in that regard, they also differ in many ways and are suitable for specific applications. Now if you’re reading this, then you probably want to know which one is better — Tor vs VPN?
VPN vs Tor: What’s the Difference
Indeed VPN and Tor are both excellent solutions for anonymity and ensuring one’s privacy online. People use them for the same reason, although they work in drastically different ways. For one thing, the Tor network relies on a series of nodes that are voluntarily operated by other users to facilitate the transfer of information over the Internet. VPNs, on the other hand, work by routing and encrypting data to a remote server.
VPN companies have control over their respective networks, which means users will have to trust them with their information. Tor networks, on the other hand, are not controlled by anybody and offers users nearly complete anonymity.
To better understand the difference between Tor and VPN, it would be best to get into the details of how each one works as well as their relative strengths and vulnerabilities as an online privacy and security tool.
What is Tor?
Tor stands for “The Onion Router” which is the original name of a non-profit project that envisioned the use of multiple layers of servers (nodes) to facilitate the anonymous transfer of information over the Internet. This means that any data you send using Tor gets routed to multiple servers before reaching its intended destination.
Now you might be thinking, isn’t that what a VPN does? Well, not exactly and while VPNs do offer a measure of privacy, Tor is different in that it has the potential to grant near complete anonymity on the Internet. How is this so?
Consider that while VPNs can stop third-parties from intercepting your information and monitoring your activities online, that protection is not ubiquitous. That is to say, that your data can be seen and logged by your VPN service provider, which can be a problem for many users.
The best thing about using Tor as a privacy tool is that you don’t have to hand over your information to anyone. This is because the latter is designed in such a way that users are almost entirely anonymous. While the Tor network does not guarantee full anonymity, it is safe to say that it is tough (if not impossible) for anybody to single out your information over a Tor network.
How Does Tor Work?
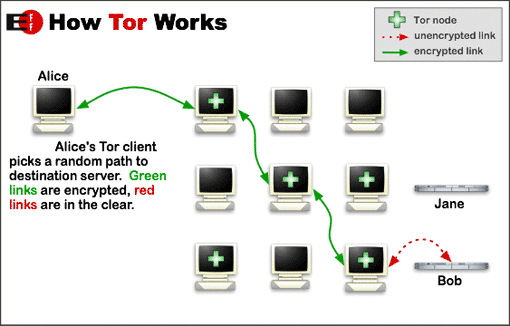
Users (Alice) can access the Tor network by using their free browser (Tor Client). Whenever a data request is placed, the Tor browser establishes a connection with a Tor server (node) which then passes the data request to another node and so on.
As you can see from the image above, the data request passes through up to 3 nodes before reaching its target destination (Bob). The response is then sent back to the user in the same manner. The use of multiple relay nodes is what safeguards the identity of Tor users.
Each node is selected at random and only has information on the IP address of the previous node and the next one in the sequence. Hence, none of the nodes that make up the Tor network know where the data request initially came from, nor are they able to associate said request with the target destination. Also, data sent through the Tor network is encrypted as it passes through the different nodes. In this manner, traffic inside the Tor network cannot be analyzed or intercepted by third-parties.
Of course, the Tor network is not foolproof and has its weaknesses, particularly with the exit node, which is the last to facilitate the transfer of information before arriving at its targeted destination. The data passing through the final node is unencrypted, so Tor users should only visit websites with a secure connection (https). Otherwise, the information may be visible to the party operating the exit node.
What Are the Pros and Cons of using Tor?
Now that you have a good idea of how the Tor network operates, we can then single out a few specific pros and cons for using the latter.
The Pros of Using Tor:
- It is free to use. The Tor project is a non-profit organization dedicated to safeguarding one’s privacy over the Internet.
- The Tor network cannot be shut down by the government and other third-parties as it is comprised and operated by thousands of volunteers.
- Hides users’ IP addresses and conceals their identity by routing data through a series of random servers.
- Defeats censorship and enables access to geo-blocked content.
The Cons of Using Tor:
- The Tor network can be extremely slow and only as good as the fastest node on the relay. This is inevitable, considering that data has to pass through multiple servers with different bandwidths. Hence Tor is generally unsuitable for any high-speed applications like P2P file sharing and video streaming.
- The exit nodes on the Tor network can be used for spying since data passing through the latter is unencrypted.
- The Tor network is only accessible through a specific browser or other applications that have an integrated Tor client. Any information sent outside these platforms is unprotected.
- No accountability on the part of volunteers operating the nodes on the Tor network. No support staff in case of technical problems.
- Not compatible with iOS (iPhone, iPod Touch or iPhone).
- The Tor network can be used to access the “Dark Web” which can get users into trouble.
What Is a VPN?
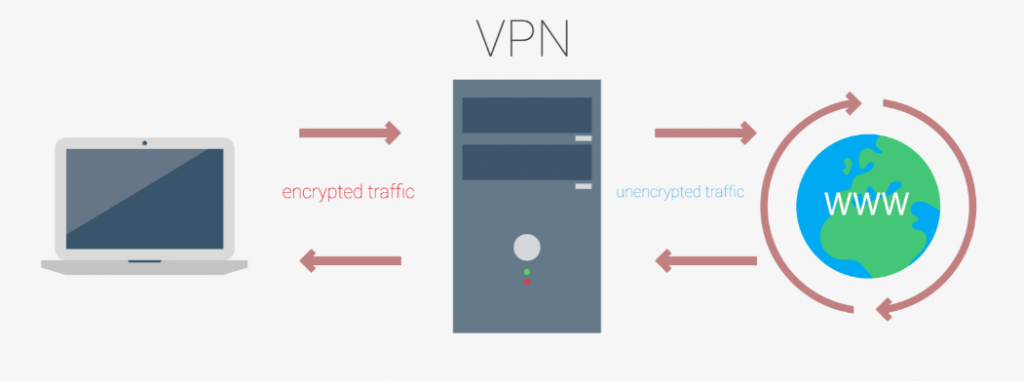
A VPN is a networking technology designed to safeguard users’ privacy online by redirecting traffic to an external server to conceal one’s IP address and encrypt data communications. Unlike Tor, users essentially “lease” the resources on a VPN server and have them send information to the targeted destination on their behalf. As a result, the computer or mobile device of VPN users are never directly in contact with the destination server.
How Does a VPN Work?
VPNs are comprised of a network of servers from multiple locations all over the world. As you can see from the image above, using a VPN involves passing internet traffic to a VPN server before reaching its intended destination (website or apps). In the same way, server responses are routed to the same VPN server and are then forwarded back to the user’s computer or mobile device.
In this manner, VPNs facilitate sending and receiving information without having to compromise their users’ location and other personally identifiable information. Also, most reputable VPN companies use secure encryption which blocks unscrupulous third-parties from stealing sensitive information, especially over public WiFi networks.
The Pros of Using a VPN:
- VPNs are faster compared to Tor because traffic is only being routed to one external server as opposed to several nodes with various bandwidths.
- While the best VPNs on the market are paid services, the premiums help support network upkeep and ensure the highest performance possible.
- VPN protection includes all connections on a user’s device and not just the browser. This includes apps, games, and other applications that involve sending information over the Internet.
- Most reputable VPN services feature an Internet kill switch that automatically disconnects users from the Internet in the event of a data leak.
The Cons of Using VPN:
- Some VPNs (mostly free ones) serve ads and collect information on users to sell to interested third-parties.
- Some VPN services log the activities of users, which can be a problem for users concerned about their privacy. Governments can exert pressure on VPN companies and force them to turn over any information they have about their users. To be safe, users are advised to opt for VPN companies with a “No Logging” policy.
- VPN users are not entirely anonymous on the Internet. Traffic goes through a VPN server, and VPN companies can see their users’ information.
- VPNs are illegal in some countries with strict Internet censorship laws (North Korea, China, United Arab Emirates, and the like).
In case, you'll choose to go with VPN, here's the list of TOP 5 VPN :
Summary
Both Tor and VPN are excellent solutions for protecting sensitive information and maintaining privacy online. The answer to the question, “VPN vs Tor, which is better?” ultimately depends on what is most suitable to your situation.
The Tor network excels at transmitting highly sensitive information where users are willing to compromise speed for higher data security. On the other hand, VPN is the more practical solution for most people as it offers complete data protection and presents a good balance between speed and security.