Most people use the internet today without batting an eye at what actually transpires each time they log on to their favorite website or Internet-based services. As users exchange data with their internet providers, there is always a risk of unscrupulous individuals/organizations keeping tabs on your activities online, stealing your sensitive information, or selling your information to other parties. This is where the use of a VPN comes into play. So what is a VPN?
VPN Meaning
In a nutshell, a VPN (a virtual private network) is a security solution that grants users secure and private access to the internet. It accomplishes this by redirecting data through an anonymous server designed to hide the sensitive user information.
Why Use a VPN?
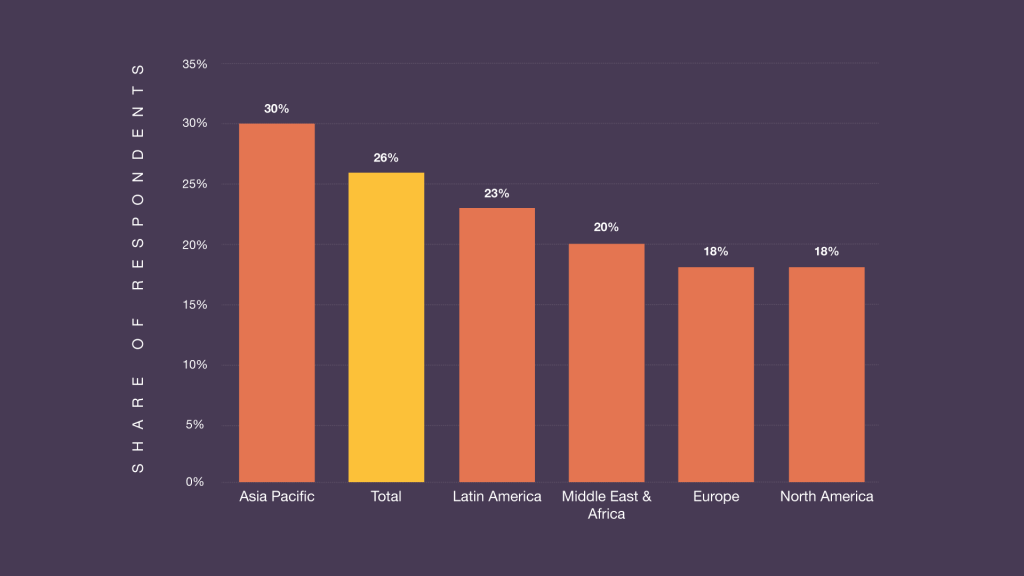
More people today are making good use of VPN services and for many good reasons. According to Statista (a statistics and studies portal), approximately 26% of internet users worldwide use a VPN to access the internet (Statista).
The latter study was conducted during the first quarter of 2018, and that number is expected to soar even higher in the next few years.
More than 50% of users get a VPN to gain access to better content for entertainment. This is because a VPN can be used to unlock content from all over the world. So, if you live in the UK and want to access content that is only available to users in the US (Netflix shows, Youtube videos, music, and the like), you can use a VPN to circumvent such restrictions.
Of course, a VPN has more to offer than simply its entertainment value. For one thing, a VPN can be used to protect one’s personal information when traveling and connecting to unfamiliar public Wi-Fi networks in airports, bus stops, and restaurants. You can never be sure that these networks are safe and are not being used to collect the personal and financial information of users. A VPN service mitigates this problem by feeding and receiving data through an encrypted channel designed to make stolen data undecipherable.
Another less common (but just as strong) argument that supports the widespread use of VPN services are cases of government restrictions that are aimed at censoring people’s access to information and services over the internet. One good example is the Egyptian Revolution of 2011 wherein the Egyptian government kept its citizens from accessing Twitter and other social media outlets online to quell the spread of information about the uprising. With a VPN enabled, users in countries such as North Korea, China, and Iran (all countries that block their citizens from accessing certain online services, including Twitter) can circumvent any restrictions and not have to worry about their government spying on their online activity.
How Does a VPN Work?
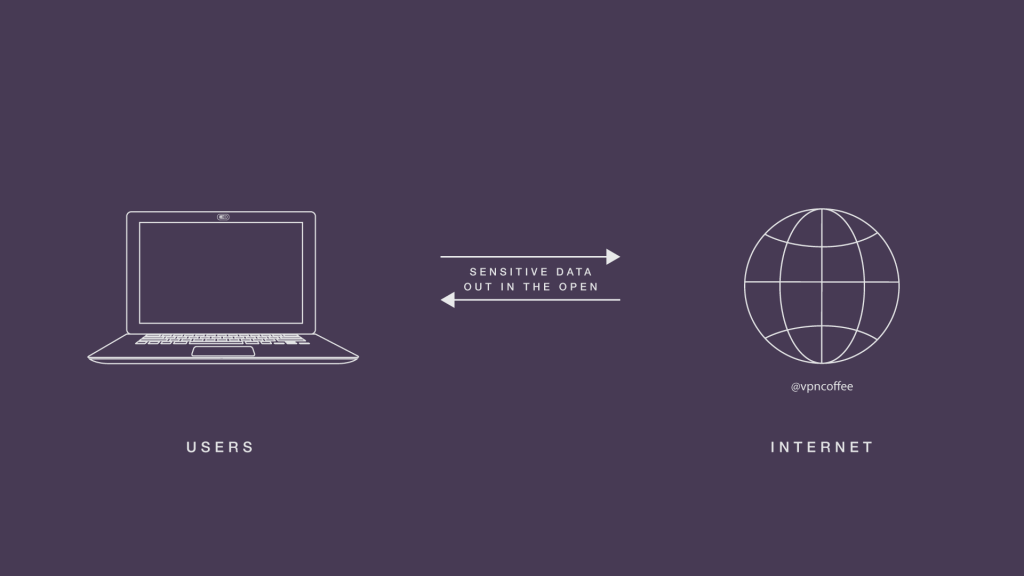
To understand how do VPN apps work, it would be best to first take a good look at what happens during a standard connection to the internet and its inherent flaws:

While the above graphic might seem to be an oversimplification, the idea that you are basically leaving sensitive data “out in the open” is fairly accurate. There are no safeguards for whatever information you are sending online. This means that anyone who knows what they are doing can simply swoop in and grab your sensitive information: personal data, passwords, credit card numbers; you get the picture.
The internet is home to millions of servers, with each one responsible for hosting one or several websites (shared servers). These servers transmit data to users that need access to them as well as talk and share information with other servers. This arrangement works well for accessing and sharing information over the internet quickly and efficiently but not so much when it comes to privacy.
Now, if you are simply surfing the web as a leisure activity and not doing anything particularly important, then there is no reason to worry. However, if you are dealing with data that is potentially valuable (online banking information, business emails, online transactions, and the like), then you will want to consider using an added layer of protection, which is precisely what a VPN offers.
How can a VPN Hide an IP Address?
Here are the basics of what changes when you add a VPN to the mix:
As you can see from the graphical representation above, VPN users are encrypting their data, which can only be read by the VPN server and vice-versa. That how VPN server works. The VPN server is the one interacting with the internet on the user’s behalf, which explains its privacy and security benefit.
Simply put, the destination server will see only the VPN server as the source of the data request, which, in turn, hides the real IP address of the VPN user. The process is designed in such a way that it is extremely difficult (if not impossible) for outsiders to pinpoint specific users as the source of any online activity. Any data intercepted between the user and the VPN server is heavily encrypted and practically useless to third parties.
How Secure is a VPN?
In this VPN guide, we'll learn how secure is VPN. As you may have already realized, a VPN-enabled internet connection is, in many ways, a lot safer to use compared to the standard unencrypted connection. So, just how secure is it? Well, there is no straight answer to this question, and it has long been the subject of much debate among security experts. Also, consider that no two VPN services are exactly alike. This is due to several factors, such as:
- The kind of VPN technology used and its accompanying limitations
- Legal and policy restrictions that regulate what users can do with VPN technology
Are VPNs Legal to Use?
For the vast majority of users, the answer is a big “yes,” although there are exceptions. The first thing people need to know about the legality of VPNs is that the jurisdiction surrounding their use is fairly recent and can be interpreted in different ways.
For the most part, what matters most when it comes to the legality of VPN use is your physical address or location. For most freedom-loving countries, such as the United States, Canada, Australia, and the UK, the use of VPNs is perfectly acceptable and even encouraged.
In contrast, the use of VPNs is typically looked down upon in countries that routinely censor the online activities of its citizens. Such countries include the following:
- Turkmenistan
- Oman
- Iraq
- United Arab Emirates
- China
- Turkey
The list above is far from exhaustive, so if the issue of legality is of particular concern to you, we recommend checking the applicable laws in your country.
VPN Protocols and Its Pros and Cons (GEEK edition)
Another factor that can influence the security of a VPN service is the protocols that it uses. These protocols determine how data is transmitted over a VPN network. The most popular VPN protocols include the following:
- Point-to-Point Tunneling Protocol (PPTP) — One of the first VPN protocols created by Microsoft and a native feature of the Windows Operating System. This VPN protocol boasts high compatibility across a wide range of internet-enabled devices and even works on old computers. The only caveat is that it is not as secure by modern standards.
- Layer 2 Tunneling Protocol (L2TP) — A step up from the old PPTP protocol and boosts security by adding “keys” for establishing a secure connection for every data tunnel. While a significant improvement from its predecessor (especially with the IPsec update), it is still not considered safe by modern standards, and there have been reports of third parties being capable of breaking through the protocol.
- Internet Key Exchange Version 2 (IKEv2) — Another VPN Protocol made by Microsoft in conjunction with Cisco. IKEv2 is an updated version of IPSec and has none of its flaws. As a result, IKEv2 offers a safer and more reliable VPN experience for users.
- Secure Socket Tunnel Protocol (SSTP) — Microsoft built the SSTP based on the SSL/TLS protocol (the standard for encrypting information over the web). It is widely regarded as one of the safest VPN protocols in use today. This protocol uses a technique called “symmetric key cryptography,” which reserves the ability to encrypt and decode data between to two parties, the sender and the receiver. The only downside is that SSTP is proprietary technology and only works on computers running Windows (Vista and higher).
- OpenVPN — Most security experts agree that this is the best VPN protocol in use today. Similar to SSTP, OpenVPN is based on the SSL/TLS architecture and uses symmetric key cryptography. The only difference is that it is open-source technology that is constantly being tweaked for improved performance by thousands of developers and is compatible with most internet-enabled devices today. The only downside is that OpenVPN is more susceptible to latency, which can only be mitigated by the use of newer and more powerful computers for VPN connections.
So What Does VPN Mean (Summary)
In conclusion, VPNs are a must-have for anyone who wants to take their online security and privacy to the next level. They offer an additional layer of protection that is not much different from any of the number of digital security practices that people are implementing: using antivirus software, not opening shady emails from unknown senders, not sharing sensitive information on social media, etc.
More people ought to use VPNs as there are practically no downsides save for the occasional slow-down in internet speeds. After all, VPN users are essentially redirecting internet data through an external server. Still, most digital security experts would agree that even that is just a small price to pay to keep your information safe in an age of rising cybersecurity threats.