VPNs have become much more accessible and popular in recent years as companies promote their service, leading with increased security as one of the biggest benefits. But can VPNs protect you from man-in-the-middle attacks on data that are becoming more and more common? Let's discuss this issue and find out how to protect your personal and financial data using a VPN.
The Most Common Man-in-the-middle Attacks
Unsecured and public WiFi networks could pose a security threat because of something called an ARP spoofing attack. These were much more common several years ago, but have become less effective in recent years so have declined in popularity among hackers.
They worked by using a computer to pretend to be a wireless hotspot, such as those found in cafes and restaurants. People would then connect to it and the hacker would be able to see all of the internet traffic being sent over that connection. If passwords were sent in plain text over an unsecured HTTP connect, the hacker would also see these.
Man-in-the-middle attacks can be performed in other ways, though.
DNS and IP spoofing can trick your computer into thinking it is connected to the right website when it actually isn’t.
Typically, a VPN will protect you against these types of attacks since your VPN will often use its own DNS to resolve domains. If it doesn’t, you should look at using a service like OpenDNS, Cloudflare, or Google Public DNS.
Hackers can also steal your cookies, which are small files used to keep you signed into websites. By stealing the cookies, they can pretend to be you and get around the password protection of your account.
Email spoofing and hijacking is also a common man-in-the-middle attack where a bad actor will monitor email traffic, looking for emails they could exploit. When they find one, they’ll send an email pretending to be a bank, senior manager, or another person of authority and ask the user to transfer money, change a password, or some other similar action.
Setting Up a VPN For Protection Against the Attacks
VPNs are usually easy to set up, with most providers offering their own software that you can download and install in minutes. What VPNs do is they create an encrypted tunnel between your computer and the server you’re connecting to. There are several different protocols that can be used including OpenVPN, L2TP, or PPTP. Each with their own pros and cons, but all serving the same basic function.
When a VPN says that it protects you when using unsecured WiFi networks, it’s the encryption that does this.
Certainly, a VPN app can be installed directly onto mobile devices as well. Whatever you're doing online, your traffic is channeled through the VPN, whether it's playing classic card games from companies like PokerStars, checking your emails through Gmail or Outlook, or streaming shows through Netflix.
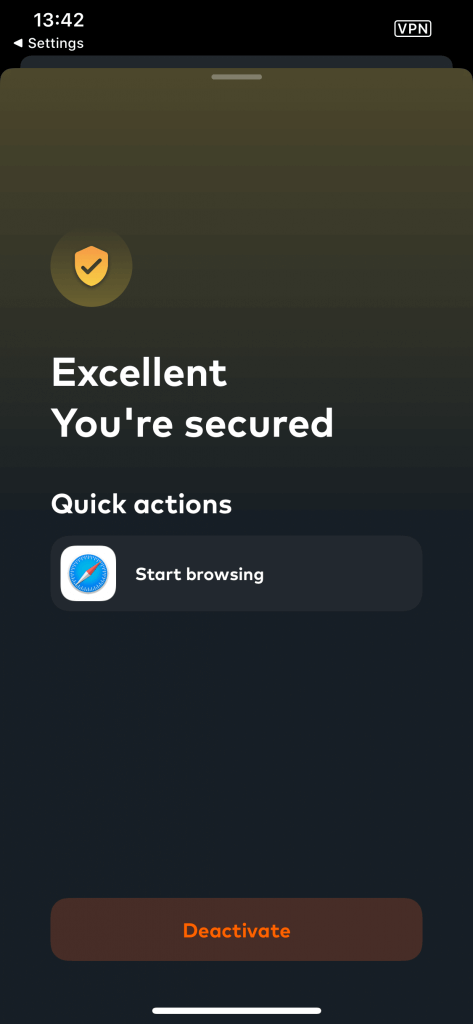
Here’s an easy step-by-step guide on setting up your VPN encryption with one of the promising newcomers, Assguard:
- Find the “Encrypt Connection” shortcut in the dashboard.
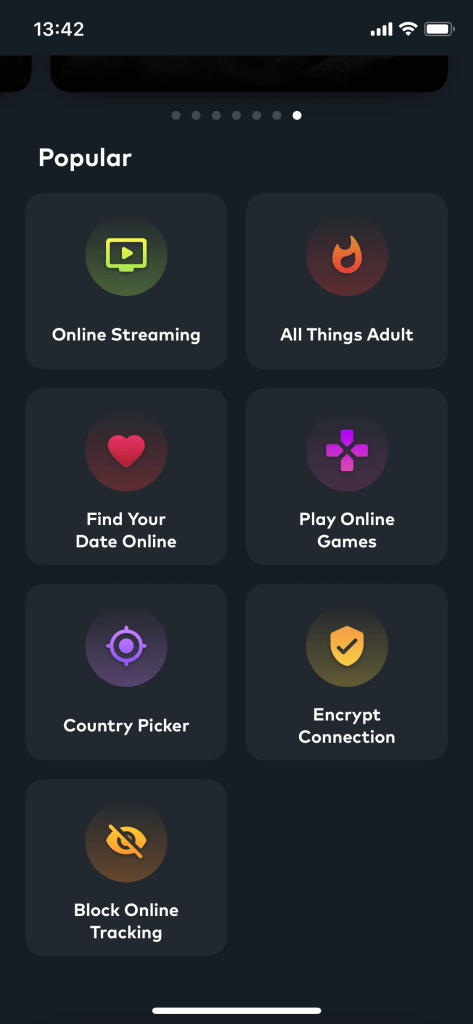
- Activate the shortcut in one tap.

- You’re encrypted. Now you can use a browser to surf securely.
Read more: Here's our list of the best VPNs for Android in 2020
Summary
A VPN is not the only tool you can use to protect yourself from man-in-the-middle attacks. Keeping your computer free from viruses with quality anti-virus software, not clicking on links in emails unless you are 100% sure it is safe. However, VPN is a good option, if you need a one-tap solution to reduce the risk of a man-in-the-middle attack — that’s exactly where to start. Altogether with checking you are accessing HTTPS websites and regularly clearing cookies, a good VPN will help you substantially protect your data from man-in-the-middle attacks.